LANtenna Attack, use network cables to create wireless signals and steal data
What is the LANtenna Attack?
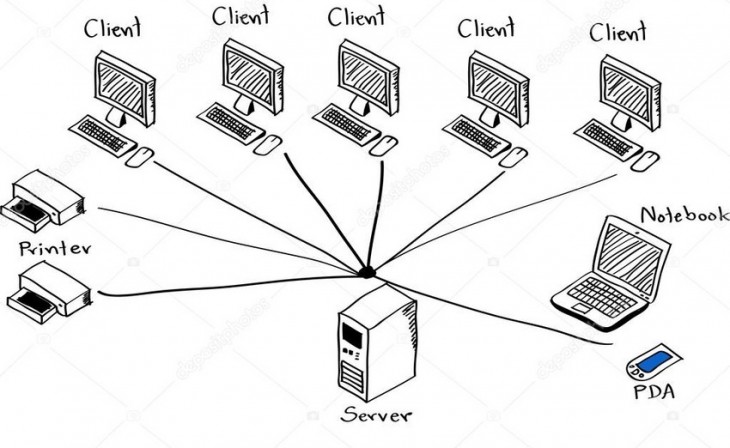
This attack consists of a mechanism to exfiltrate data that uses Ethernet network cables as a transmission antenna, in this way, information can be sent to a receiver. Of course, this transmitting antenna is capable of diverting highly confidential information that travels over the Ethernet network cable to the receiver, with the aim of stealing very valuable information. Generally, network cables are used to protect ourselves against wireless attacks, but with this attack, what came to solve the problem "of the air", makes it become the fundamental piece of the attack.
This very new data exfiltration technique allows malicious code in computers to accumulate confidential data that is later to be exfiltered or sent to a receiver, to later encode it through radio waves using Ethernet network cables as an antenna. Malicious code can be run in a normal user-mode process, no administrator permissions are required, and it could also operate successfully within a virtual machine. Transmitted radio signals can be intercepted by a nearby software-defined radio receiver (SDR) and completely wirelessly, logically this system does not have too much range, but it does have enough to put sensitive and confidential information on computers at risk.
The entire data exfiltration process is done with any wireless interface disabled or physically removed, that is, there is no native sender. This same security researcher has already demonstrated highly unconventional ways of leaking confidential computer data, such as when he designed a method that employs small changes in the brightness of an LCD screen, or when he demonstrated how malware could use a PC's power supply to reproduce sounds and use it as a secondary out-of-band “speaker”. Finally, this same researcher was also able to take advantage of WiFi signals as a covert channel to exfiltrate confidential information without requiring the presence of WiFi hardware on the target computer.
How this attack works
In order to carry out this attack, it is necessary to use malware on the target computer with an air gap, to induce the Ethernet network cable to generate electromagnetic emissions in the 125MHz frequency bands that are then modulated and intercepted by the nearby receiver. In tests carried out by this researcher, it was found that information can be sent at a distance of about 2 meters, more than enough to steal a large amount of information passively.
In the following video you can see a demonstration of how this data exfiltration technique works:
Of course, as with other attacks of this style, it is necessary to infect the victim's computer in the target network, through any vector: a pen drive, an email using social networks or directly infect the pen drives from their manufacture with the goal of spying on a larger scale.
How can I avoid this attack?
Security researchers have proposed some recommendations to avoid or mitigate this attack, the first thing is to prohibit the use of radio receivers in the surroundings of the network, and of course, to monitor the activity of the link layer of the network card that we have to avoid covert channels. Signals can also be blocked using metallic shielding to limit interference from electromagnetic fields that occur in network cables.
Although a distance of 2 meters may seem very little, the researchers have indicated that with dedicated and expensive antennas they could have a greater distance, and could easily reach tens of meters with some cables, therefore, this attack could put anyone in danger. Bearing in mind that it is necessary to infect a computer with malware, it is very necessary to monitor what can be installed on corporate computers, in order to minimize as much as possible that an attacker can infect us.